How to Spot — and Defeat — eDiscovery Dirty Tricks



By our loose count, there are about a dozen different federal, state and model ethics rules regarding eDiscovery, all reminding you to play fair. But come on—we know lawyers. Some are bound to push, pull, prod, and otherwise test the outer boundaries of those rules. Not you, of course. Not anyone at your firm. But some.
So, what can you do when you come across underhanded tactics, objectionable moves, and downright dirty tricks? We recently gathered together several eDiscovery experts for a webinar addressing just that question. Here are some of the highlights, though you’ll want to check out the entire webinar as well (available below.)
Getting Out From Under a Document Dump
First out of the gate is an oldie and a baddie: the document dump. Rebecca Rakoski, co-founder and managing partner of XPan Law Group, a boutique law firm focused exclusively on cybersecurity and data privacy, kicked off the document dump discussion with some sage advice: Know your data and be “the most prepared person in the room.” The first step to defeating a document dump, after all, is to prevent one from happening in the first place.
To that point, Rakoski advises:
Understand what you’re doing, know where your documents are, discover how they are sorted, determine how they’re stored, locate what your client is doing with them, and get a handle on that in a proactive way.
You want to know exactly where everything is, how it’s stored, how you can cull it down so you’re only getting to the heart of the documents that you need and not just the documents you’re going to be asking for from the other side, but what you have yourself to produce part of your discovery obligations.
Knowing your documents will help you get ahead of the opposing party when it comes to discovery, whether it’s assessing your case, crafting an effective ESI agreement, or preparing for the meet and confer.
When you go into that meet and confer meeting, you don't want to be sitting there going, “I don't know where these documents are...” You want to be very proactive in front of the judge so that you’re the person that the judge looks to when you have an electronic discovery question. Know what you have and what you're going to be asking for.
You’ve got to get a handle on your own production, the opposing party’s production, and, perhaps most importantly, the judge. Most judges, especially if you’re in federal court, will want a meet and confer on all discovery issues early on. “You want to be very proactive in front of the judge,” Rakoski said, “so that you’re the person that the judge looks to when you have an electronic discovery question.”
Being prepared and knowledgeable will discourage the other side from even trying to take advantage of you, will mean that you can spot a document dump before or right when it happens, and that the judge might side with you on how deal with opposing counsel who dumps.
And if the dump does happen? “Don’t panic,” the panelists agreed. “There are fantastic tools that you can use nowadays to cull down large document productions,” Rakoski noted, tools that allow you to cull through the unnecessary documents to find those that matter.
And, if worse comes to worse, you can always turn to the court.
If the other side is not willing to play nicely in the sandbox, the last thing you can do is go to the judge. We all have an affirmative and ethical obligation to try and get along with our adversary. Nobody wants a situation, least of all federal judges, where they're sitting there and ask “How long is it going to take to review the billion documents that just got dumped on you?”
Be prepared. Play nice. And, if need be, pull the judge in for help. (And it doesn’t hurt to have the best eDiscovery platforms at your disposal—along with the best tips for using that software—if you need to sift through virtual mountains of docs.
Resisting (and Supporting) Proportionality Objections
If you’ve been paying attention at all to discovery in recent years, you’re probably familiar proportionality and the explosion of proportionality objections, both justified and not-so-justified. The proportionality requirements can be found in Rule 26, which limits discovery to “any nonprivileged matter that is relevant to any party's claim or defense and proportional to the needs of the case.” (Emphasis added—by us and the 2015 amendments to the Federal Rules of Civil Procedure.)
Parties, and courts as well, are tasked with limiting discovery based on “the importance of the issues at stake in the action, the amount in controversy, the parties’ relative access to relevant information, the parties’ resources, the importance of the discovery in resolving the issues, and whether the burden or expense of the proposed discovery outweighs its likely benefit.”
Today, objections to discovery orders based on proportionality are quickly replacing claims that discovery is overly burdensome or unlikely to yield relevant evidence, according to judges.
So how do you deal with proportionality issues? Unsurprisingly, Rakoski’s earlier advice comes in handy. Brian Wolfinger, formerly a detective with the Philadelphia Police Department, longtime eDiscovery expert, and currently CTO at Everest Technologies, says preparation and knowledge of the data pools at play is essential. Understanding the volume of data that could be relevant, both in total and per custodian, can be key to providing the information needed to support, or push back against, proportionality claims.
You can use technology as a lever to formulate your arguments about what is a proportional delivery of data based on your environment, the data volumes your client possesses, the systems that are in use and how they can be accessed, and what sampling have you done to create real statistics.
You can put that in front of the judge and to your opponent to say this is what we believe is proportional based on the systems we have in place.
In addition to raw numbers, Rakoski recommends tying arguments about proportionality back to the claims and defenses at issue in the matter.
You can go back to making some of the more traditional arguments. Support it with the data that you've got, but also look at the claims and defenses. Is this an essential part of my claim? Do I really need to prove this? Do I really need a defense in this area instead of throwing everything up against the wall and seeing what's going to stick?
Once you’re in front of the judge, you need the data and arguments to be trustworthy. Rakoski notes that large corporations claiming they don’t have the staff or resources to “effectively litigate in an electronic discovery context” aren’t likely to sway judicial opinion. “You want to look at resources, how you're going to support your claims, and what documents you need if you're going again,” she explained.
And if there is a strong connection between document requests and the claims made, or if there is no data to support contentions that discovery is disproportional, then weaponized proportionality objections should be much easier to defeat.
Denials of Custody and Control: To Have and to Hold and to Produce (Or Not)
What can you do when facing a potentially specious claim that a party does not have custody and control over the requested information?
The guiding light is fairly simple: Follow the rules. “We can answer many questions in the rulebook,” according to Rakoski. “You need to look at what your standards are. You need to look at what you're doing, how you're doing it, and whether you are complying with the rules.”
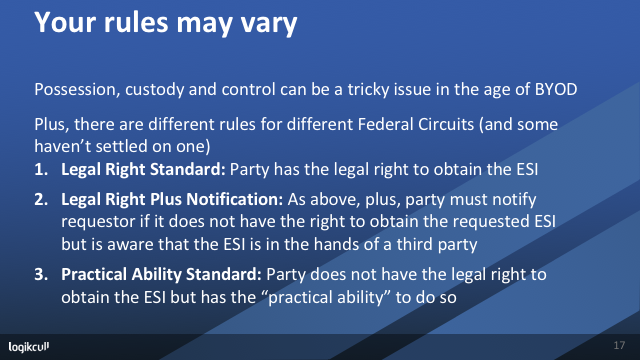
Michael Simon, principal at the eDiscovery consultancy Seventh Samurai, points to two recent eDiscovery cases, Van Zant v. Pyle (as in Ronnie Van Zant and Artimus Pyle, of Lynyrd Skynyrd fame) and Brown v. Teller, for guidance on handling possession, custody, and control issues. And the applicable rules, Simon reminds us, vary by circuit.
But he also gives a few words of advice. “[D]o not go claiming that you do not have access to your own data,” Simon warned. You should also be wary of getting caught carrying control agreements unbeknownst to the judge. “You do not want to be in the position of having to answer the judge on that … It's not pretty. You don't want to be there.”
When Spoliation Just Accidentally Happens
Spoliation happens. And when it happens, the spoliating party often claims innocence, that the destruction of data was accidental and in error, and what does it matter since it wouldn’t have impacted the case anyway. Sometimes that’s true. Sometimes it’s not. So, what can you do?
When facing any potential spoliation, particularly spoliation of evidence that could have been damaging to the possessing party, start with the basics. Wolfinger advises a six-step approach.
- Has ESI even been lost or is it recoverable?
- Should the ESI in question have been preserved given the circumstances?
- Did the party fail to take reasonable steps to preserve?
- Can the ESI be restored or replaced?
- Was there a specific intent to deprive based on the actions taken?
- Was there prejudice to the other party by being deprived of this data?
The central element courts will look at when examining these questions (and deciding whether and how to punish parties guilty of aiding and abetting spoliation) is intent, and even inferred intent.
But don’t be too quick to allege intent to deprive, Wolfinger cautions. “You have to be really careful before you allege bad intent,” he advises, “until you really understand the technical underpinnings of the organization and what was actually done so far. There are a lot of reasonable explanations why you don't need to look at everything.”
Want more ways to defeat eDiscovery dirty tricks? Watch the webinar on-demand know.
Learning With Logikcull
Browse our latest resources for innovative legal teams like yours
Stay in the know
Get the latest news, expert guidance, and interviews delivered straight to your inbox so you're always one step ahead.

Get the latest updates

Want to see it work?
Request a demo today.
Managing FOIA requests with limited staff, strict deadlines, and pressure to protect sensitive data?
Logikcull is built for this.



