Data Preservation and Legal Hold

Litigation Hold Basics
What Is a Legal Hold?
A legal hold, also known as a litigation hold, is the process by which organizations preserve potentially relevant information when litigation is pending or reasonably anticipated. By issuing a legal hold, organizations notify custodians about their duty not to delete ESI or physical documents relevant to a case.
Since under FRCP Rule 37(e) (the section that governs the spoliation of electronic evidence) organizations have a duty to "under take reasonable actions" to preserve information that is relevant to the case when they anticipate litigation or another type of formal dispute, they need to be able to prove that they have taken "reasonable and good-faith efforts" to ensure that data is not deleted after the triggering event occurs. A triggering event is the event or occurrence that precipitates the party to begin preserving information (for example, when expecting another organization or an employee to initiate litigation.)
Therefore, having a legal hold process in place and using a legal hold-specific tool is crucial to show defensible and good faith efforts to preserve evidence.
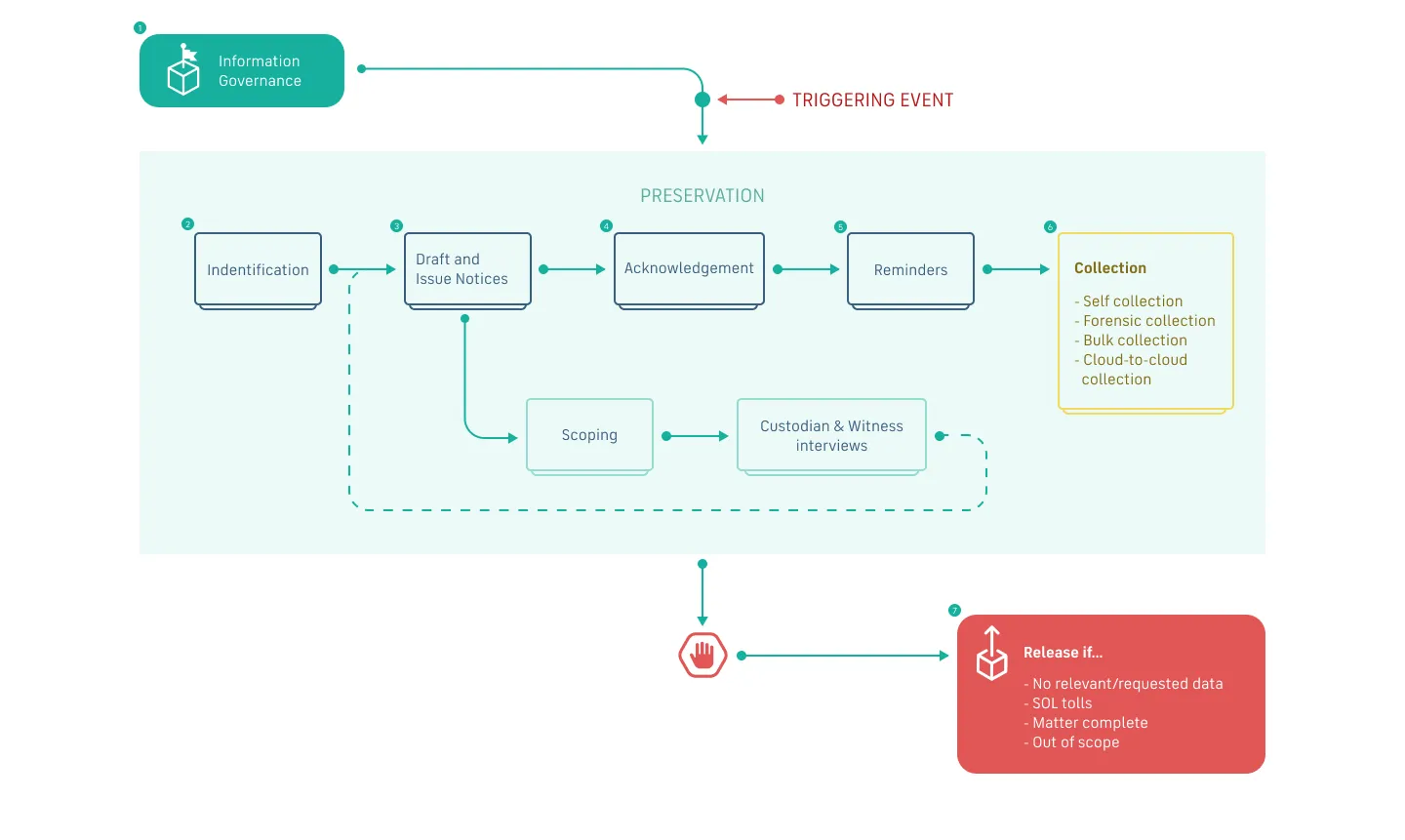
Although it's common to think about legal holds as the notification that is sent to custodians in order to preserve information, the legal hold process actually consists of multiple steps:
Identification of information to be preserved:
This is usually the first step in creating a legal hold. The legal team must determine which information could be potentially relevant to a matter. Nowadays, it’s common for this data to be electronically stored information (or “ESI”), but it might also include physical documents, like logbooks and paper files.
Identification of custodians:
A custodian is the person who personally possesses and is in charge of the information that needs to be preserved. Before issuing the hold, legal teams usually work with the IT department to identify all custodians relevant to the case. Custodians can also be “silent custodians”, that is, people in the organization whose data is preserved without getting a notification about it. This type of custodians is frequent in internal investigations, for example.
Issuance of a legal hold notice:
The legal hold notice is the communication sent to all custodians letting them know that they’re on hold and specifying which information needs to be preserved. This is a key part of the legal hold process that we’ll cover in more detail later.
Reminder notices:
Reminders should be sent to ensure custodians remember they’re still under a legal hold. Oftentimes, reminders are also needed to make sure custodians acknowledge their legal hold obligations.
Release of the legal hold:
Once the legal matter ends, you need to let custodians know that their duty to preserve has ended. Having a sound release process is important so that no custodians are released from their obligations when they shouldn’t, and no custodians stay on hold forever.
Below, we will dive more deeply into all the important aspects about legal holds and best practices in managing them.
Corporate Legal Hold Policy
In order to minimize the risk of spoliation sanctions, it’s good practice for organizations to have a corporate legal hold policy, where the goals, different steps, and any other aspects of the legal hold process are clearly laid out.
The main goal of the legal hold policy is to ensure a consistent and defensible approach to the preservation obligation. And while this obligation might be well known by legal teams and high-level management, it’s usually not familiar to most employees, including potential custodians of relevant ESI. Therefore, another goal of a litigation hold policy is to help employees understand the duty to preserve information and the potential consequences for the entire organization for failing to comply with this obligation.
A legal hold policy usually covers:
- The preservation duty
- The definition and scope of triggering events
- The notification system of potential trigger events
- The different types of ESI and their locations
- The main agents involved in the legal hold process
- The steps to take when creating and issuing a legal hold
For reference, here’s an example of a legal hold policy from the American Board of Pediatrics.
There is no “one size fits all” solution when it comes to corporate legal hold policies. Each organization needs to find the set of procedures that work best for their specific characteristics like industry, data architecture, retention policies, organizational hierarchy, etc.
However, when developed and implemented the right way, a legal hold policy can significantly improve the organization’s ability to respond and react to its preservation obligations. The key is to keep everyone informed of their role within the organization’s compliance obligations to minimize the risks associated with litigation.
In this insightful webinar, Lindsay Kolar, Corporate Paralegal at Gordon Food Service, goes over the 6 most common challenges legal holds present, and how to meet them successfully with the right processes and tools.
The Legal Duty to Preserve Potential Evidence
Legal holds arise from a common-law duty to avoid the spoliation of evidence. That duty stretches back to 1722 and the case of Armory v. Delamirie, a dispute between a young chimney sweep and a goldsmith over a found jewel. Since then, the requirements to avoid spoliation have slowly evolved over hundreds of years of case law, which eventually resulted in today’s legal hold requirements.
Although there is no federal rule requiring the implementation of legal holds, and the concept is a fairly recent development, the practical requirements of data preservation have been well fleshed out incase law over the past decade, following Judge Shira Scheindlin’s historic rulings in Zubulake v. UBS Warburg, a case that is regarded as marking the beginning of modern eDiscovery.
In Zubulake, Judge Scheindlin made it clear that parties have an obligation to conduct legal preservation of relevant information as soon as litigation is imminent. However, the process of arriving at that determination—gauging when litigation is “imminent” or "reasonably anticipated" and deciding what qualifies as “potentially relevant information”—can be more complex than it seems…
When Is the Duty to Preserve Triggered?
The most critical step in the legal hold process is determining when the duty to preserve information begins. As established by Zubulake and many other cases, a legal hold is triggered when litigation is “reasonably anticipated.” But what does “reasonably anticipated” actually mean?
Unfortunately, there is no perfect standard for interpreting the phrase. It’s as ambiguous as it sounds. When evidence is lost or the scope of preservation is otherwise questioned, courts tend to weigh other factors, such as whether parties acted with good faith and performed a reasonable evaluation of relevant facts at the time of preservation, to determine whether sanctions are appropriate.
Therefore, it’s important to develop a sound process to identify preservation triggers and issue legal holds accordingly, rather than just wait for litigation to happen, which is a risky practice still followed by many organizations.
Factors influencing when litigation is reasonably anticipated:
- Explicit communication
- Receipt of summons or complaint
- Subpoenas
- Cease-and-desist letters
- Local regulations
- Specific events, like a major defect in a company’s product
- Preservation orders
- Credible threats of litigation
On the plaintiff’s side, intentional acts such as sending a cease-and-desist letter are enough to trigger preservation obligations. But the duty may arise earlier than that. In some cases, courts have held that a plaintiff is under a duty to preserve either as soon as they determine that legal action is appropriate or when they decide to bring an action.
The trigger for defendants can seem nebulous at times. Receipt of written notice from the other party would definitely trigger a duty to preserve, but courts disagree on how certain the recipient must be that litigation will actually occur. Generally speaking, the duty to preserve does not require that the threat of litigation be “unequivocal.” A letter threatening litigation could be sufficient to prompt preservation procedures, for example.
In the most clear-cut cases, the duty to preserve is triggered by explicit communication of impending litigation, such as service of process, subpoena, or written or verbal notice. Receipt of notice by an employee or another agent generally triggers preservation for companies.
Additionally, preservation obligations can be triggered by other circumstances, such as local regulations or a preservation order already entered in another case.
However, the threat of litigation must be at least somewhat credible to trigger a duty to preserve. Aimless grumbling shouldn’t bring companies to a grinding halt. As one court explains, “it is not reasonably foreseeable [sic] that every internal employment complaint may result in litigation if not resolved to the employee’s satisfaction.” Courts have long held that, if the notice is merely an “equivocal statement of discontent,” then litigation may not qualify as “reasonably anticipated,” and deletion procedures can continue. (CacheLa Poudre Feeds, LLC v. Land O' Lakes, Inc., 2007 WL 684001 (D. Colo. Mar.2, 2007))
That being said, companies cannot simply ignore vague threats to avoid preservation. If the threat level of litigation is unclear, organizations have an obligation to investigate the situation before purging their files.
Determining exactly when the duty to preserve kicks in can get complicated. But recent amendments to FRCP Rule (37)(e), have brought a new level of predictability to the process—and bestowed renewed power on defensible procedures, such as properly administered legal hold notices. In fact, 2015 amendments to the Federal Rules of Civil Procedure have led to a reduction of 35% in spoliation sanctions.
Legal Hold Process Step-By-Step
Getting Started On Your Legal Hold
Once you have identified an event that triggers a duty to preserve potentially relevant ESI, you need to make sure you issue a legal hold as soon as possible. But before you can even draft and circulate a legal hold notice, there are a few things you need to determine:
- What information needs to be preserved
- Where does this information live
- Who are the relevant custodians
- How to determine the scope of the information that needs to be preserved so that it’s not too burdensome for custodians
When ESI is involved (that is, in 99% of cases nowadays),your IT or legal operations teams are great allies in helping you locate information sources and custodians. Having a robust information governance program in place is also key in easily identifying the location of potentially relevant ESI and who is ultimately responsible for its preservation.
In terms of deciding the scope of the information that needs to be preserved, keep in mind these factors:
- The nature of the issues raised in the matter
- The accessibility of the information
- The probative value of the information
- The relative burdens and costs of the preservation effort
To better understand all the steps and lifecycle of a legal hold, see the diagram below:
Where Will You Find Potentially Relevant Information?
When you’re under a duty to preserve, you need to act diligently and in good faith to make sure no potentially relevant information is destroyed. This information can come in different forms—from electronic data, to physical documents and tangible things—and be stored in multiple locations, such as email, desktop drives, portable devices, shared drives, tablets, smartphones, and document management systems, and also dusty drawers and archived folders.
Nowadays, most of the potentially responsive information is electronically stored information or ESI. The most common way to locate potentially responsive ESI is through custodians, the individuals who personally possess the information. Examples of custodian data sources are: email, personal storage on hardware devices or cloud accounts, allocated storage, data storage, data associated with social networking sites used by the custodian, tablets, smartphones, or even private web-based email accounts.
However, non-custodian ESI is a critical type of ESI, as well. Examples of non-custodian data sources include: databases, cloud storage databases hosted by third parties, and shared network storage locations.
These are some of the most common types of ESI and their usual locations:
- Emails
Users of corporate computers usually have emails stored on one or more email servers. These servers may be physical hardware managed by IT staff, but more often than not they live on virtual servers leased from a cloud provider, like Microsoft Exchange. A third potential source is a Software as a Service (SaaS) offering from a cloud provider, which are ubiquitous. Webmail may be as simple as a single user’s Gmail account or, like the Microsoft 365product, a complete replication of an enterprise email environment. On desktops and laptops, email is found locally (on the user’s hard drive) in container files with the file extensions .pst and .ost for Microsoft Outlook users or .nsf for Lotus Notes users, for example. Each user may be expected to have a substantial volume of archived email spread across several on- and offline sources.
- Chats and instant messages
Chat data from applications like Slack, Google Chat or Microsoft Teams has turned into a highly relevant source of ESI, especially as more teams turn to remote work, where once in-person conversations now take place over collaboration apps. These tools usually come with preservation and exporting features, so the biggest challenge with this type of ESI usually lies in the review process.
- Word-processed documents, spreadsheets, and presentations
Custodians generate a lot of content in the form of productivity documents like Microsoft Word documents, Excel spreadsheets, PowerPoint presentations, and the like. These may be stored locally, i.e., in a folder on the C: or D: drive of the user’s computer or in an area reserved to them on a network file server and mapped to a drive letter on the user's local machine. The user sees a lettered drive indistinguishable from a local drive, but on the latter, all data resides on a server, where it can be regularly backed up. This is called the user's network share or file share.
However, thanks to cloud services like Google Workspace or Microsoft 365,productivity documents can also be created and stored online, where they’reusually accessible through the built-in preservation tools of these serviceslike Google Vault.
- Social media content
Data generated in social networking sites like Facebook, Twitter, Instagram has turned into a critical source of potentially relevant ESI. With more than 1.28 billion people logging into Facebook alone every day, the amount of data produced in the more than 150 social networking sites available is almost unmeasurable. For cases in areas such as insurance fraud, IP infringement, and even terrorism, social media evidence is playing acritical role today, so lawyers need to become familiar with best practices to preserve and collect social media evidence.
- Video, audio, and image files
Multimedia data has become a more relevant type of ESI in recent years. Similar to word-processed documents, it can be found in a wide variety of sources, from local storage locations like hard drives or local folders, to cloud locations, like Dropbox or Google Drive, and even on social media sites, like YouTube or TikTok.
Other relevant types and locations of ESI include:
• Online banking, credit card, and other relevant account records.
• Accounting application data, often found in applications like QuickBooks, NetSuite, Sage, etc.
• Databases (e.g., Access, Oracle, SQL Server data, SAP.)
• Contact and Customer Relationship Management (CRM) data(stored in software like Salesforce, Outlook, MS Dynamics.)
• Calendar, journaling and diary application data (found in Outlook PST, Google Calendar, blog posts, etc.)
• Online access data like browsing history and other online activity logs.
How to Issue a Legal Hold
Best Practices for Drafting and Issuing a Legal Hold
Once the information that needs to be preserved and all custodians have been identified, the next step is to draft and issue a litigation hold notice.
While it’s good practice to have email templates and a streamlined process in place to issue legal holds as efficiently as possible, a legal hold notice must be a thoughtful document tailored to the needs of each case.
Although there are no specific legal requirements for the structure or the content of a legal hold notification, there are certainly a series of best practices that you can follow when drafting a legal hold.
Legal Hold Best Practices Checklist:
Make it timely:
In a world of automatic deletion, timing is everything, and failure to issue a timely legal hold can put you at risk of sanctions. Courts have found that “failure to adopt good practices is a factor in the determination of whether discovery sanctions should be issued.” A thoughtful legal hold police and a legal hold automation tool can help you issue a legal hold as quickly as possible after the triggering event.
Put it in writing:
An oral threat of litigation can trigger preservation, but issuing only a verbal hold notice does not count as taking “reasonable steps ”to actually preserve relevant information. To be safe, write it down.
Make it clear and specific:
Not everyone reading your hold notice is a lawyer. The point of a legal hold is to ensure that custodians comply with their obligation to preserve relevant data. Make sure your notice is not full of legalese, clearly establishes the specific information that needs to be preserved, including details about the documents’ names, dates, and offers relevant examples to custodians.
Explain the matter at issue:
It’s important that custodians understand the scope of the matter at issue so that they have more context on why it is so crucial that they comply with their duty to preserve. In some cases, knowing what the matter is about can also help custodians determine whether they have further potentially relevant ESI that should be preserved.
Ask for a notice of receipt—and follow up with custodians that don’t send acknowledgment:
If any data goes missing, you’ll want to have hard evidence of preservation efforts. Implementing a legal hold is an essential first step, but you also want to demonstrate that the hold actually reached relevant custodians (and more importantly, that they understood their obligations at the time). Always ask custodians to acknowledge receipt of the legal hold notification, and follow up with them consistently until they do so.
Offer help:
Your legal hold notice should also offer an easy way for the custodian to get in touch with the legal team for any questions or concerns.
Revise, revise, revise:
An obvious—but sometimes overlooked—step. Make sure you’re not forgetting any important detail on your notification and that you’re including all relevant custodians. If possible, get an extra set of eyes on it before issuing the hold.
Document everything:
To make the legal hold process as defensible as possible, keep track of every action consistently, like emails sent, acknowledgments received, follow-ups, etc. We’ll cover this in more detail later on.
Download a printable version of the legal holds best practices checklist here.
Other Key Litigation Hold Procedures
A thorough legal hold process shouldn’t end after the hold has been issued. Many matters can be open for long periods of time, so it’s important to make sure custodians don’t mistakenly assume that an active hold is no longer in effect, while making sure they’re also properly notified when their obligation to preserve is over.
Some important steps to take while the legal hold is still active are:
- Send reminders to custodians that don’t acknowledge receipt of the legal hold notice: To have a defensible process, you'll want to do more than just issue a hold. You should be able to demonstrate that custodians were aware of their obligation to preserve.
- Remind custodians that the hold is still active: Custodians are busy employees, just like you, and they can forget about an ongoing hold if not reminded about it. Keep a consistent reminder schedule that restates their preservation duty. This doesn’t need to be a manual process, however. The right legal hold software can easily automate your reminders during the life of a hold.
- Conduct periodic reviews of the legal hold: The scope of your legal hold might change as new sources of information are found or when certain events occur. Make sure to review the scope of your hold frequency and consider adding amendments, if necessary (and notify custodians accordingly!)
Legal Hold Release Notice: When the Obligation to Preserve Is Over
Your legal hold process is not complete if it doesn’t include provisions for releasing the hold when the duty to preserve is over. A legal hold release notice enables your organization to resume its normal retention policies and schedule, and lets custodians—both internal and any third-parties—return to their regular workflows without fear of spoliation.
Here’s an example of a legal hold release notice from the Association of Corporate Counsel.
When releasing a legal hold, it’s important to verify the information or custodians released are not subject to other preservation obligations through a different legal hold. Having a robust and centralized tracking system of all legal holds is essential here.
Legal Hold Compliance
How to Ensure Data Preservation Compliance with a Legal Hold
As mentioned earlier, sending frequent reminders to custodians is one way to minimize the chances of data spoliation.
But apart from forgetful custodians, there are other challenges that can get in the way of successfully preserving all relevant data for a case:
Terminations and Changing Custodians:
This turns into a bigger challenge the bigger an organization is and the longer a legal hold lasts. Both when determining who the original custodians are and reassessing the scope of a legal hold, you need to account for any potential changes in employee statuses such as leaves of absence, promotions, new roles, etc.
Solution: It’s important to work closely with your HR team to verify custodians and get notified about any important changes throughout the lifetime of a legal hold. One great way to always stay abreast of any relevant changes in custodians’ status is to use a legal holds software that integrates with your employee database or employee management system.
Custodian and Legal Holds Overlaps:
As mentioned above, some matters can go on for long periods of time, while some custodians may possess ESI relevant to multiple matters, so it’s common for companies to have several legal holds active at once and for certain custodians to be subject to multiple holds. For example, Gordon Food Service, the largest family-owned food distributor in the U.S., issues an average of 10 legal holds per month, and some of them can last several years. It is therefore not uncommon to have one custodian involved in multiple holds at a time, which can create management challenges if you don’t have effective tracking and clear communication.
Solution: A diligent and reliable tracking method of your legal holds is the best way to navigate the risks associated with overlapping holds and custodians. Traditionally, this has largely been a spreadsheet-based process, but organizations are more and more relying on available legal hold technology to automate this process and make it less prone to human error.
Negligent or Unresponsive Custodians:
No matter how clear, specific and easy-to-act-on your legal hold notification might be, you will surely need to deal with custodians who ignore you or even fail to comply with their preservation obligations altogether—even after acknowledging receipt of the legal hold notice. And while this can be one of the most frustrating parts of the legal hold process, there are certain actions you can take that don’t involve manually sending dozens of reminders per week.
Solution: Before escalating a situation with an unresponsive custodian, you should try to exhaust any method of direct communication with them. To make your life easier, you can keep a consistent follow-up schedule and make sure you notify unresponsive custodians a certain number of times before taking further action. There are legal hold tools that allow you to automate follow-up emails, which makes this process much easier. However, if after multiple follow-ups custodians keep ignoring you, an escalation notice might be necessary. This means notifying the custodian’s manager about their inaction, alerting them about the risks the company might be exposed to, and asking them to intervene.
Ensuring Preservation by Third-Parties
If there’s any third party that maintains data on your behalf, may still be considered to be under your own possession, custody, and control. If you have access to that data, you are also responsible for preserving and potentially producing it. However, identifying third-party data and making sure third parties meet their obligations to preserve aren’t always straightforward tasks.
Solution: A robust information governance program should help your organization determine where data lives, and the obligations that third parties need to comply with in order to manage your company’s data.
Monitor Compliance Regularly
When it comes to ensuring all custodians are complying with their preservation obligations, consistent monitoring is key. Apart from regular reminders and asking for periodic acknowledgments of the hold obligations, compliance training sessions, where the negative consequences for noncompliance are clearly laid down, can be powerful tools to ensure compliance.
This monitoring process is more effective when tailored to the custodian. Consider your custodians’ technical expertise and familiarity with your preservation policies, as well as their understanding of the importance of legal hold compliance in determining how frequent and detailed reminders need to be.
Numerous decisions have shown that it’s not enough to issue a hold notice and rely on individuals to meet their preservation obligations (See, e.g., Concord Boat Corp. v. Brunswick Corp.,207 F.3d 1039 (8th Cir. 2000).) Courts have found that counsel has a duty to monitor—and sometimes even intervene—in a party’s efforts to comply with their preservation obligations.
How Are ‘Possession, Custody, and Control’ Determined?
When an organization knows litigation is coming, corporate defendants must preserve anything under their “possession, custody, or control”—but how far does that “control” go? Are corporations responsible for ensuring that employees and other non-parties fully comply with preservation practices?
The short answer is yes. Certainly, companies have an obligation to identify key custodians and make sure they preserve their data. But the duty often goes further than that. Named parties may also be responsible for ensuring subpoenaed or otherwise notified non-parties, including employees, also comply with the terms of relevant legal holds. That may include obtaining discovery into employee's personal devices, for example.
The “possession, custody, and control” standard is established by Rule45 of the Federal Rules of Civil Procedure. Federal courts have taken different approaches to interpreting that requirement, leading to three general standards:
- The Legal Right Standard: Data is considered under a party’s possession, custody, and control when the party has a legal right to obtain the ESI. This standard is applied in the Third, Fifth, Sixth, Seventh, Eighth, Ninth, Tenth, and Eleventh Circuits.
- The Legal Right Plus Notification Standard: Data is considered under a party’s possession, custody, and control when the party has a legal right to obtain the ESI, plus, if no such right exists, the party has been put on notice that the ESI is in the hands of a third party and thus, must notify its adversary. This standard is applied in the First, Fourth, Sixth, and Tenth Circuits.
- The Practical Ability Standard: Data is considered under a party’s possession, custody, and control when, regardless of whether the party has a legal right to the data, it has the practical ability to obtain the ESI. This standard is applied in the Second, Fourth, Eighth, Tenth, Eleventh, and D.C. Circuits.
How To Document Your Legal Hold Process
How to Ensure Data Preservation Compliance with a Legal Hold
In the context of legal holds, your main focus should be to create a process that is defensible, meaning that your opposition, judge, jury, or regulator will regard it as appropriate and sufficiently thorough. While perfection is not required, your actions will need to be reasonable given the information available at the time of the action.
That’s why it’s important that you document the preservation notice process to show when and how a legal hold was issued, acknowledged, and whether it was properly maintained from the moment of the triggering event. You should keep track of all the custodians and actions taken throughout the process—hold issuance, custodian acknowledgments, hold revisions, reminders, and legal hold release. The most efficient way to do this is by using legal hold automation software to get all your actions automatically logged.
Once your legal hold notice is distributed, you will require recipients to acknowledge receipt of the communication and understanding of their preservation duty. This can be tracked through an email reply or by adding a special link to your email that recipients can just click on to acknowledge that they understand and will comply with the legal hold requirements. This option is usually available only on legal hold software.
Any reminders to recipients reiterating that the hold and its instructions are still in place and that potentially relevant information should not be altered should also be tracked.
Lastly, it’s also important to document when the hold was released and why (i.e. what was the event that made the preservation duty no longer necessary?).
You’ll want to make sure that your legal hold process and technology is capable of recording and reporting on the following details, for individual matters and custodians:
In addition to documenting actions taken throughout the legal hold process, it’s also important to keep track of the reason behind your actions. For example, if the scope of the hold changes at some point and new custodians are notified or existing custodians released, you should include an explanation of why that decision was made.
All these being said, you may never need to disclose this information. However, if opposing parties were to challenge your organization’s preservation efforts, a well-documented legal hold process and implementation efforts can be effective methods of demonstrating your organization has taken reasonable steps to comply with its preservation obligations.
Picking The Right Legal Hold Software
Managing legal holds using spreadsheets is not efficient nor secure. More and more, legal teams are relying on existing technology to streamline their legal holds and have most of the steps covered in this guide done automatically for them.
When evaluating legal hold software, look for a solution that meets these requirements:
Customizable:
Create and send legal hold notices based on built-in templates with your own messaging. This can really help speed up the process of issuing the hold.
Easy to distribute:
Selecting existing custodians or adding new ones should be a simple process.
Automated:
Set your notice and reminders and let the software handle the rest.
Trackable:
See at a glance your legal hold activity in a dashboard that updates in real-time.
Collaborative:
Communicate across teams in order to preserve data.
Easy to release:
Simply and easily lift your holds when data no longer needs to be preserved.
Scalable:
Find a product that can scale to your needs, whether you’re managing one hold or hundreds.
Predictable:
Litigation is expensive. Your legal hold software shouldn’t be.
Comprehensive:
Look for a solution that integrates smoothly with your eDiscovery process, so when a hold transforms into a full-blown investigation or litigation, you can instantly turn your hold into a discovery matter.
The Ultimate Guide to eDiscovery
Want to see it in action? Request a demo today
Our team of product specialists will show you how to make Logikcull work for your specific needs and help you save thousands in discovery.
